-
DeHashed: View leaked credentials
Amongst the most popular and advanced security and anti-fraud tools available online, DeHashed is one of the most progressive and popular. Through the DeHashed platform, end users can search for and regain info from hacked databases.
This platform makes it possible for end users to recover their leaked information rapidly and prevent the information from being misused by hackers or crackers. It’s one of the fastest and most weighty data breach search engines out there. Its upfront interface and ease of use make it popular with users who want to trace their leaked information quickly and easily.
For More Info visit official webpage: https://www.dehashed.com/
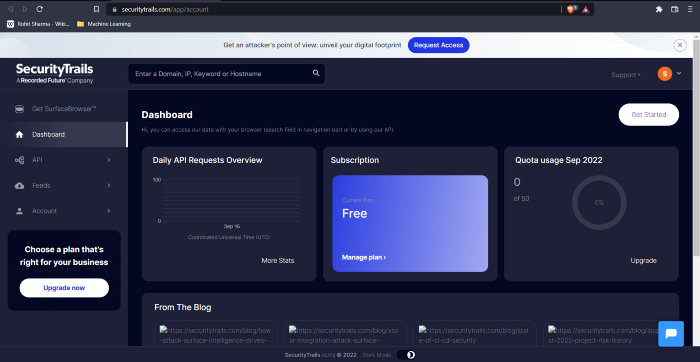
- Security Trails: Extensive DNS data
With SecurityTrails, administrations can see how their threat attack surface is — the networks and servers that are reachable from the wider internet — by aggregation and keeping vast amounts of current and past internet records, such as domain names, registration data, and DNS data.
For More Info visit official webpage: https://securitytrails.com/
-
DorkSearch: Really fast Google dorking
You can use DorkSearch to find prebuilt patterns for different categories of Google Dorks.
For More Info visit official webpage https://dorksearch.com/
-
ExploitDB: Archive of various exploits
An Exploit Database is an archive of publicly available exploits and vulnerabilities in software developed for vulnerability researchers and penetration testers.
Through direct submissions, mailing lists, and other public sources, it assembles the most comprehensive collection of exploits, shellcodes, and papers, and presents them in a easily navigable and freely accessible format.
For More Info visit official webpage: https://www.exploit-db.com/
-
ZoomEye: Gather information about targets
A search engine developed by Chinese company Knownsec Inc., It uses maps to collect data and analyze fingerprints from open devices and web services. The current version is Version 3. Its first version was released in 2013.
For More Info visit official webpage https://www.zoomeye.org
-
Pulsedive: Search for threat intelligence
At this search engine you can find more then 35 million searchable IOCs, free of charge, which are generated using user submissions and threat intelligence feeds. Pulsedive is an analyst-centered threat intelligence platform. Using Pulsedive’s free threat intelligence data set, highlight IPs, domains, and URLs on any website to enrich them.
For More Info visit official webpage: https://pulsedive.com/
-
GrayHatWarefare: Search public S3 buckets
There are currently 48,623 open S3 buckets in GrayhatWarfare’s free tool, which is a searchable database created by software engineer GrayhatWarfare.
As a popular way to cache content, Amazon’s S3 cloud storage, or Simple Storage Service, is used by both the public and private sectors. Files are assigned buckets that are secure and private by default, but can easily be set to be public by the user.
For More Info visit official webpage: https://grayhatwarfare.com/
-
PolySwarm: Scan files and URLs for threats
As a launchpad for new technologies and innovative threat detection methods, PolySwarm competes to keep you safe in real time.
A network of threat detection engines powers PolySwarm. Combining commercial engines with specialized solutions, it offers wide coverage.
For More Info visit official webpage: https://polyswarm.network/
-
Fofa: Search for various threat intelligence
With FOFA, users can find IP assets easily, match network assets quickly, and speed up the follow-up process. This cyberspace search engine is developed by BAIMAOHUI.
There are many examples, including vulnerability scope analysis, application distribution statistics, popularity ranking statistics, and so on.
For More Info visit official webpage : https://fofa.so/
-
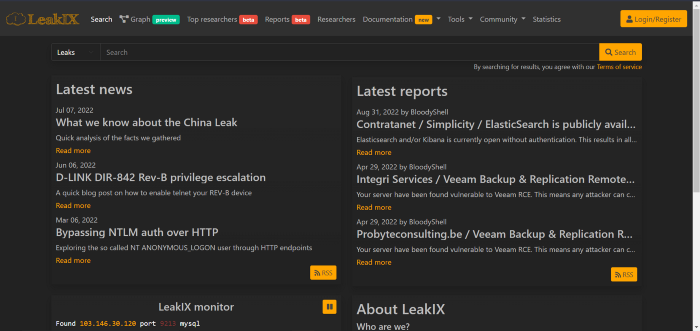
LeakIX: Search publicly indexed information
There are some capabilities that separate LeakIX from Shodan, both visually and based on queries used, but the web-based platform offers a very similar visual experience to Shodan.
What I think the platform’s value is is its ability to provide insight into compromised devices, servers, and database schemas on the internet, now yes, Shodan tags ‘compromised’ servers in much the same way, but it’s not as comprehensive.
For More Info visit official webpage: https://leakix.net/
-
DNSDumpster: Search for DNS records quickly
An application for which help to DNS reconnaissance on target networks.
It provides end users with information such as geographical data, host details, email addresses, and formats that can be used to learn more about the networks.
For More Info visit official webpage: https://dnsdumpster.com/
-
FullHunt: Search and discovery attack surfaces
It is a database that contains all attack surfaces on the Internet, meaning
it is capable of identifying all the attack surfaces on the network, monitoring them for infection, and continuously scanning them for vulnerabilities.
For More Info visit official webpage: https://fullhunt.io/
-
AlienVault: Extensive threat intelligence feed
You can get a feature-rich open source SIEM with AlienVault OSSIM, Open Source Security Information and Event Management (SIEM). In response to the lack of open source security solutions,
AlienVault OSSIM was developed by security engineers to address the issue many security professionals face: Without basic security controls, a SIEM is virtually useless for security visibility, regardless of whether it is open source or commercial.
For More Info visit official webpage: https://otx.alienvault.com/
-
ONYPHE: Collects cyber-threat intelligence data
By crawling various Internet sources or listening to background noise,
Onyphe collects open-source and cyber threat intelligence data for their Cyber Defense Search Engine.
For More Info visit official webpage: https://www.onyphe.io/
-
Grep App: Search across a half million git repos
The Grep.app will display a list of repositories that correspond to the search.
Now you can find those elusive coders on GitHub quite effectively.
For More Info visit official webpage: https://grep.app/